Penetration Testing
Module Guide
Explore every security test our platform runs. Each module targets specific vulnerability classes using industry-standard techniques and tools.
🕷️ Web Crawler & Discovery
Discovers pages, endpoints, forms, API routes, and JavaScript files to map the full attack surface.The Crawler module is the foundation of every scan. It performs a breadth-first traversal of your web application to discover all reachable pages, forms, API endpoints, and JavaScript files. This attack surface map is used by every subsequent module to know where to test. The crawler respects configured depth limits and skip paths.
How It Works
- 1 Starts from the target URL and begins BFS crawling
- 2 Extracts links, forms, and API endpoints from HTML
- 3 Parses JavaScript files for additional endpoints
- 4 Identifies input fields, parameters, and form actions
- 5 Builds a comprehensive site map within configured depth
- 6 Shares discovered attack surface with all other modules
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Discovered pages & endpoints | Info | CWE-200 |
| Forms with input fields | Info | — |
| Exposed API routes | Low | CWE-200 |
| JavaScript files with endpoints | Info | — |
| Hidden or unlinked pages | Low | CWE-538 |
💉 SQL Injection Testing
Tests forms, URL parameters, headers, and API endpoints for SQL injection vulnerabilities.The SQL Injection module tests all discovered input vectors for SQL injection vulnerabilities using multiple techniques including error-based, boolean-blind, and time-based injection. It tests form fields, URL parameters, HTTP headers, and API endpoints. Optionally integrates with sqlmap for deeper analysis.
How It Works
- 1 Identifies all injectable parameters from crawled data
- 2 Tests with error-based SQL injection payloads
- 3 Performs boolean-blind injection tests
- 4 Executes time-based blind injection checks
- 5 Tests HTTP headers (User-Agent, Referer, etc.)
- 6 Validates findings and assesses impact
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Error-based SQL Injection | Critical | CWE-89 |
| Blind SQL Injection (boolean) | Critical | CWE-89 |
| Time-based Blind SQL Injection | Critical | CWE-89 |
| SQL Injection via HTTP Headers | High | CWE-89 |
| SQL Injection in API Endpoints | Critical | CWE-89 |
⚡ Cross-Site Scripting (XSS)
Tests for reflected, stored, and DOM-based XSS using 30+ payloads and filter bypasses.The XSS module tests for reflected, stored, and DOM-based Cross-Site Scripting vulnerabilities. It uses over 30 specialized payloads including filter bypass techniques, encoding tricks, and context-aware injection. Also checks for Server-Side Template Injection (SSTI) patterns.
How It Works
- 1 Identifies all reflection points from crawled pages
- 2 Tests reflected XSS with 30+ specialized payloads
- 3 Attempts filter and WAF bypass techniques
- 4 Checks for DOM-based XSS patterns in JavaScript
- 5 Tests for stored XSS via form submissions
- 6 Checks for SSTI (Server-Side Template Injection)
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Reflected XSS | High | CWE-79 |
| Stored XSS | Critical | CWE-79 |
| DOM-based XSS | High | CWE-79 |
| Server-Side Template Injection | Critical | CWE-1336 |
| XSS Filter Bypass | High | CWE-79 |
🔑 JWT Token Analysis
Tests for algorithm confusion, weak secrets, role escalation, and token manipulation attacks.The JWT module analyzes JSON Web Tokens used by your application for common security weaknesses. It tests for algorithm confusion attacks (none algorithm, RS256 to HS256 downgrade), brute-forces weak signing secrets, attempts role/privilege escalation through claim manipulation, and checks token expiration settings.
How It Works
- 1 Discovers JWT tokens in cookies, headers, and responses
- 2 Decodes token structure and analyzes claims
- 3 Tests algorithm confusion (none, HS256/RS256 swap)
- 4 Brute-forces signing secret with common passwords
- 5 Attempts role escalation via claim manipulation
- 6 Checks token expiry and key confusion attacks
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Algorithm Confusion (none algorithm) | Critical | CWE-345 |
| Weak JWT Signing Secret | Critical | CWE-521 |
| Role/Privilege Escalation via Claims | Critical | CWE-269 |
| Missing Token Expiration | Medium | CWE-613 |
| Algorithm Downgrade (RS256→HS256) | High | CWE-327 |
🔐 Authentication & Access Control
Tests for default credentials, rate limiting, CORS, IDOR, CSRF, and auth bypass vulnerabilities.The Authentication module tests your application's authentication and access control mechanisms. It checks for default credentials on common admin paths, tests rate limiting on login forms, analyzes CORS configurations, tests for Insecure Direct Object References (IDOR), Cross-Site Request Forgery (CSRF) protections, and authentication bypass techniques.
How It Works
- 1 Scans for common admin and login paths
- 2 Tests default credentials on discovered login forms
- 3 Checks login rate limiting and brute-force protections
- 4 Analyzes CORS headers for misconfigurations
- 5 Tests for IDOR on authenticated endpoints
- 6 Checks CSRF token presence and validation
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Default Credentials | Critical | CWE-798 |
| Missing Rate Limiting | High | CWE-307 |
| CORS Misconfiguration | High | CWE-942 |
| Insecure Direct Object Reference | High | CWE-639 |
| Missing CSRF Protection | Medium | CWE-352 |
| Authentication Bypass | Critical | CWE-287 |
📋 HTTP Security Headers & Config
Checks HSTS, CSP, cookie security, TLS configuration, and server information disclosure.The Security Headers module audits your application's HTTP security headers and server configuration against industry best practices. It checks for HSTS, Content Security Policy, X-Content-Type-Options, cookie security flags, server version disclosure, and TLS/SSL configuration strength using testssl.sh or sslyze integration.
How It Works
- 1 Fetches HTTP response headers from all discovered pages
- 2 Checks for missing security headers (HSTS, CSP, etc.)
- 3 Analyzes cookie flags (Secure, HttpOnly, SameSite)
- 4 Tests for server version information disclosure
- 5 Evaluates TLS/SSL configuration strength
- 6 Compares against OWASP security header recommendations
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Missing HSTS Header | Medium | CWE-319 |
| Missing Content Security Policy | Medium | CWE-1021 |
| Insecure Cookie Flags | Medium | CWE-614 |
| Server Version Disclosure | Low | CWE-200 |
| Weak TLS Configuration | High | CWE-326 |
| Missing X-Content-Type-Options | Low | CWE-693 |
🔀 Data Manipulation & Input Validation
Tests for NoSQL injection, mass assignment, parameter tampering, file upload attacks, and path traversal.The Data Manipulation module tests how your application handles various types of malicious input beyond traditional SQL injection. It covers NoSQL injection (MongoDB), mass assignment vulnerabilities, parameter tampering, malicious file uploads, and path traversal / Local File Inclusion (LFI) attacks.
How It Works
- 1 Tests API endpoints for NoSQL injection payloads
- 2 Checks for mass assignment by adding extra parameters
- 3 Tests parameter tampering on price/quantity fields
- 4 Uploads malicious files to test upload validation
- 5 Tests path traversal and LFI payloads
- 6 Validates input sanitization across all endpoints
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| NoSQL Injection | Critical | CWE-943 |
| Mass Assignment | High | CWE-915 |
| Parameter Tampering | High | CWE-472 |
| Unrestricted File Upload | Critical | CWE-434 |
| Path Traversal / LFI | Critical | CWE-22 |
🌐 SSRF & Command Injection
Tests URL-accepting parameters for SSRF and OS command injection including blind/time-based techniques.The SSRF & Command Injection module targets server-side request forgery and OS command injection vulnerabilities. It identifies parameters that accept URLs and tests them with SSRF payloads targeting localhost, internal networks, and cloud metadata endpoints. It also tests for direct and blind/time-based command injection across all input vectors.
How It Works
- 1 Identifies URL-accepting parameters and form fields
- 2 Tests SSRF with localhost and internal IP payloads
- 3 Tests cloud metadata endpoint access (AWS, GCP, Azure)
- 4 Tests direct OS command injection payloads
- 5 Performs blind command injection with time-based detection
- 6 Tests various shell metacharacter bypass techniques
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Server-Side Request Forgery (SSRF) | Critical | CWE-918 |
| Cloud Metadata Access via SSRF | Critical | CWE-918 |
| OS Command Injection | Critical | CWE-78 |
| Blind Command Injection | Critical | CWE-78 |
| Internal Network Access | High | CWE-918 |
🔧 API Fuzzing & External Tools
Directory brute-forcing, Nikto, Nuclei integration, HTTP method testing, and XXE detection.The Fuzzing module completes the scan by leveraging specialized external tools and fuzzing techniques. It performs directory brute-forcing using gobuster, dirb, or feroxbuster to find hidden files and directories. Runs Nikto for known vulnerability checks, Nuclei for template-based detection, tests HTTP methods for misconfigurations, and checks for XML External Entity (XXE) vulnerabilities.
How It Works
- 1 Runs directory brute-forcing (gobuster/dirb/feroxbuster)
- 2 Executes Nikto scan for known vulnerabilities
- 3 Runs Nuclei with vulnerability detection templates
- 4 Tests HTTP methods (PUT, DELETE, TRACE, etc.)
- 5 Checks for XXE in XML-accepting endpoints
- 6 Aggregates tool results into unified findings
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Hidden Directories & Files | Medium | CWE-538 |
| Known Vulnerabilities (Nikto) | High | Various |
| Template-based Detections (Nuclei) | High | Various |
| Dangerous HTTP Methods Enabled | Medium | CWE-749 |
| XML External Entity (XXE) | Critical | CWE-611 |
| Sensitive File Exposure | High | CWE-538 |
🔓 OAuth2 / OIDC Misconfiguration
Tests OAuth 2.0 and OpenID Connect for redirect URI bypass, CSRF via state, PKCE, token leakage, and code reuse.Tests OAuth 2.0 and OpenID Connect implementations for common misconfigurations that can lead to account takeover, token theft, and authorisation bypass. Analyses OIDC discovery endpoints, redirect URI validation, state parameter usage, PKCE support, and token handling.
How It Works
- 1 Fetches OIDC discovery and checks signing algorithms
- 2 Tests 20+ redirect URI bypass payloads
- 3 Checks for missing state parameter (CSRF)
- 4 Validates PKCE enforcement on authorization flow
- 5 Tests for token leakage via Referer and logs
- 6 Attempts authorization code reuse attacks
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Redirect URI Validation Bypass | Critical | CWE-601 |
| Missing State Parameter (CSRF) | High | CWE-346 |
| PKCE Not Enforced | High | CWE-345 |
| Token Leakage via Referer | High | CWE-200 |
| Authorization Code Reuse | High | CWE-294 |
| Weak Signing Algorithm in OIDC | Medium | CWE-327 |
⚠️ Insecure Deserialization
Tests for insecure deserialization across Java, Python, PHP, and .NET stacks including gadget chains and polymorphic types.Tests for insecure deserialization vulnerabilities across Java, Python, PHP, and .NET technology stacks. Insecure deserialization can lead to remote code execution, denial of service, and privilege escalation. Maps to OWASP Top 10 A8:2017 and SOC 2 PI1.1.
How It Works
- 1 Sends Java ysoserial gadget chain payloads
- 2 Tests Python pickle deserialization via __reduce__
- 3 Tests PHP unserialize on URL params and POST bodies
- 4 Sends .NET BinaryFormatter and JSON polymorphic payloads
- 5 Detects error signatures indicating unsafe deserialization
- 6 Reports affected endpoints with technology stack details
Expected Findings
| Finding | Severity | CWE |
|---|---|---|
| Java Deserialization (ysoserial) | Critical | CWE-502 |
| Python Pickle Deserialization | Critical | CWE-502 |
| PHP Unserialize Injection | Critical | CWE-502 |
| .NET BinaryFormatter Deserialization | Critical | CWE-502 |
| JSON Polymorphic Type Abuse | High | CWE-502 |
Comprehensive Security Reports
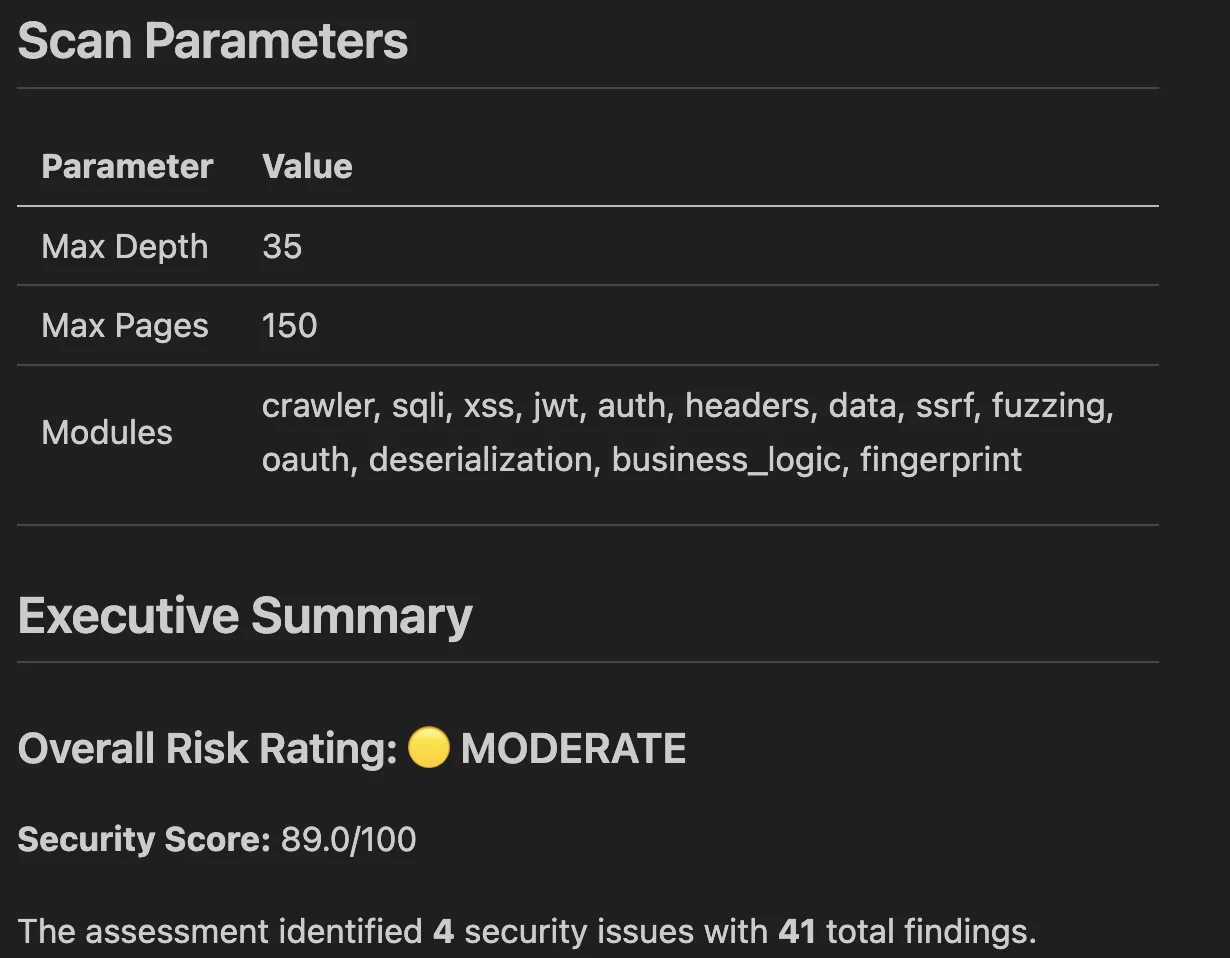
After all modules complete, SaaS PenTest generates a detailed penetration test report that aggregates all findings. Reports are sorted by severity, include CWE references, affected endpoints, evidence, and remediation guidance.
- ✓ PDF and Markdown formats
- ✓ Executive summary with risk overview
- ✓ Findings sorted by severity (Critical → Info)
- ✓ CWE/CVE references per finding
- ✓ Remediation steps and best practices
- ✓ Share with team or download
 Report — PDF penetration test report with findings by severity
Report — PDF penetration test report with findings by severity
Ready to Test Your Application?
Create an account and run a comprehensive list of security modules against your web application in minutes.